MyInfo API (3.1.0)
Download OpenAPI specification:Download
MyInfo REST APIs for retrieving Person data.
Note - this specification is subject to changes based on evolution of the APIs.
3.1.0 (16 September 2019)
- New data items available:
cpfemployerspartialuinfin
- New 'subentity' parameter in person API that allows traceability to platform's client who will be receiving the person data.
- Provide clarity on the handling of
housingtype&hdbtype
- New data items available:
3.0.2 (10 May 2019)
- Upper case all desc values for:
- Driving Licence : Comstatus, PDL and QDL Validity
- Children Birth Records: Sex
- Sponsored Children Records: Sex, Residential Status
- Person: Sex, Residential Status
- Upper case all desc values for:
- 3.0.1 (15 Apr 2019)
- Removed
serialnofrompdlandqdlunderdrivinglicenceas it is not in use. - Updated description for Understanding the Data Structure
- Removed
3.0.0 (31 Mar 2019)
IMPORTANT NOTE: response format for
personAPI has substantial changes from the previous version. Please refer to Understanding the Data Structure for details.- APIs updated to v3:
- Test:
- /com/v3/authorise
- /com/v3/token
- /com/v3/person/{uinfin}/
- /com/v3/person-sample/{uinfin}/
- Production:
- /com/v3/authorise
- /com/v3/token
- /com/v3/person/{uinfin}/
- Test:
- Response changes from JWE to JWE wrapping JWS
- Security header (changes in Authorization header parameters)
- Streamline header parameters to app_id, nonce, signature_method (RS256), signature, timestamp
- Standardisation of 'code', 'desc' and 'value' of all data items.
- New data items available:
- employmentsector
- passtype
- hdbownership
- sponsoredchildrenrecords
- vehicles
- drivinglicence
- Rename data items:
- workpassstatus -> passstatus
- workpassexpirydate -> passexpirydate
- Changes to the following data item to include "type" discriminator to discriminate local and foreign address. Format is significantly different between the two.
- regadd
- billadd
- mailadd
- Deprecated vehno attribute
- Updated scheduled downtimes: sandbox and test enviroments will no longer have any scheduled downtimes.
- APIs updated to v3:
2.2.1 (28 Dec 2018)
- QR only login:
- changes to support QR only login.
login_typeparameter must be provided in the authorise API call.
- changes to support QR only login.
- QR only login:
2.2.0 (05 Dec 2018)
Base URL changes:
- Production Environment: from
myinfosg.api.gov.sgtoapi.myinfo.gov.sg - Test Environment: from
myinfosgstg.api.gov.sg/testtotest.api.myinfo.gov.sg - Sandbox Environment: from
myinfosgstg.api.gov.sg/devtosandbox.api.myinfo.gov.sg
- Production Environment: from
Security header (
.e.no longer needed in basestring)- Before v2.2.0, when crafting the basestring of the security header, an additional
.e.is required in the domain name: e.g.myinfosgstg.api.gov.sg->myinfosgstg.e.api.gov.sg.
Note: This is no longer required - In v2.2.0, when crafting the basestring of the security header, the url in the basestring is the same as the one you call; e.g.
api.myinfo.gov.sg - For more details, please refer to Security > Request Signing section for updated instructions.
- Before v2.2.0, when crafting the basestring of the security header, an additional
Data items deprecated:
- assessyear
- assessableincome
New data items available:
- noa(basic)
- noa
- noahistory(basic)
- noahistory
Added link to MyInfo demo app under Support section for easy reference.
2.1.1 (21 September 2018)
- updated error codes and descriptions for
tokenandpersonAPIs for better clarity when troubleshooting.
- updated error codes and descriptions for
2.1.0 (01 July 2018)
- "relationship" data item is deprecated
- New data items available:
- childrenbirthrecords
- marriagecertno
- countryofmarriage
- workpassstatus
- workpassexpirydate
2.0.0 (20 April 2018)
- Base URL changed from:
- myinfo.api.gov.sg to myinfosg.api.gov.sg (Production) and myinfosgstg.api.gov.sg (Staging)
- APIs updated to v2:
- Staging:
- /test/v2/authorise
- /test/v2/token
- /test/v2/person/{uinfin}/
- Production:
- /v2/authorise
- /v2/token
- /v2/person/{uinfin}/
- Staging:
- Updated responses for v2 Person APIs:
- Response format will be JSON Web Encryption (JWE) instead of JSON Web Signature (JWS).
- Base URL changed from:
The RESTful API adopts Semantic Versioning 2.0.0 for releases, and every new release of the API increments the version numbers in the following format:
{MAJOR}.{MINOR}.{PATCH}{MAJOR}number introduces incompatible API changes with previous{MAJOR}number also resets{MINOR}to0,{MINOR}number introduces new functionalities or information that are backward compatible also resets{PATCH}to0, and{PATCH}number introduces bug fixes and remains backward compatible.
Pre-release or draft versions, when provided, are denoted by appended hypen - with a series of separate identifiers {LABEL}-{VERSION} following the {PATCH} number. Such releases are unstable and may not provide the intended compatibility with the specification in draft status.
Serving as notice, the RESTful API in version 2.X.X are incompatible with version 1.X.X releases.
Despite backward compatibility in {MINOR} or {PATCH} releases, API consumers are best to evaluate and determine their implementation does not disrupt use-case requirements.
The following diagram illustrates how the integration with MyInfo APIs work:

As shown above, your application will be interfacing with our API Gateway to integrate successfully with MyInfo.
The RESTful APIs are provided in both testing and live environments, and are accessible over the Internet via HTTPS.
Consumers are to ensure firewall clearance on their edge network nodes for connecting to the APIs.
The convention used by API endpoints' URLs is in the following format:
https://{ENV_DOMAIN_NAME}/{CONTEXT}/{VERSION}/{RESOURCE}{ENV_DOMAIN_NAME}indicates MyInfo's API domain names - respectively:sandbox.api.myinfo.gov.sg, ortest.api.myinfo.gov.sg, orapi.myinfo.gov.sg, following
/{CONTEXT}, indicates the context of the API call =/com/{VERSION}indicates the endpoint's release{MAJOR}version number path - for this release =/v3/{RESOURCE}indicates the API resource path name. Any additional query string parameters are appended as needed.
1. Sandbox Environment
The sandbox environment is used for your testing when developing your prototype. The Person-Sample and Person API will return test data described in https://api.singpass.gov.sg/library/myinfo/developers/resources-personas.
Note:
- Domain Name:
sandbox.api.myinfo.gov.sg - PKI digital signature is not required for all APIs.
- Authorization Bearer access token is not required in Person-Sample API.
- Authorization Bearer access token is required in Person API.
2. Test Environment
The test enviroment is used for testing your application with the full security measures required in production. The Person API will return test data described in https://api.singpass.gov.sg/library/myinfo/developers/resources-personas.
Note:
- Domain Name:
test.api.myinfo.gov.sg - PKI digital signature is required for Token and Person APIs.
Refer to Security > Request Signing for the steps to sign your request. - Authorization Bearer access token is required in Person API.
3. Production Environment
The production enviroment is the actual live environment with full security measures and live data.
Note:
- Domain Name:
api.myinfo.gov.sg - PKI digital signature is required for Token and Person APIs.
Refer to Security > Request Signing for the steps to sign your request. - Authorization Bearer access token is required in Person API.
The following are the scheduled downtimes for the various environments:
Production Environment
- CPFB data - Everyday 5:00am to 5:30am
- IRAS data - Every Wed, 2:00am to 6:00am, Every Sun, 2:00am to 8:30am
- Once a month, Sunday 12:00 am to 8:00 am (date to be advised)
Test Environment
- none
Sandbox Environment
- none
MyInfo's API gateway supports accessing of APIs via the following interfaces:
HTTP version 1.1 connection over TLS (Transport Layer Security) version 1.1 or 1.2 standards, and ciphersuites:
- using AES (Advanced Encryption Standard) and SHA (Secure Hash Algorithm),
- on either GCM (Galois/Counter Mode) or CBC (Cipher Block Chaining) mode.
Below is the list of recommended cipher suites that you may use:
- TLS_RSA_WITH_AES_256_GCM_SHA384
- TLS_RSA_WITH_AES_128_GCM_SHA256
- TLS_RSA_WITH_AES_256_CBC_SHA256
- TLS_RSA_WITH_AES_256_CBC_SHA
- TLS_RSA_WITH_AES_128_CBC_SHA256
- TLS_RSA_WITH_AES_128_CBC_SHA
IMPORTANT: ensure your server supports TLS 1.1 or 1.2 and supports a cipher suite in the list above.
Accessing the RESTful APIs using prior versions of TLS and/or unsupported ciphersuites will result in connectivity errors. MyInfo's API gateway does not support 2-way TLS client nor mutual authentication.
API HTTP interface features:
- JSON (JavaScript Object Notation) is the supported data media format and indicated in
Content-Typeheaderapplication/json, also Content-Lengthheader is omitted by havingTransfer-Encodingheaderchunkedemitted for streaming data, and- GZip (GNU Zip) response compression is supported by opt-in
Accept-Encoding: gzipand indicated inContent-Encodingheadergzip.
MyInfo APIs use OAuth2.0 authorisation code flow to perform authentication & authorisation.
The sequence diagram below illustrates the steps involved in integrating your application with our APIs:

The flow consists of 3 APIs:
Authorise
- This will trigger the SingPass login and consent page. Once successful, your application will receive the authorisation code via your callback url.
Token
- Call this server-to-server API with a valid authorisation code to get the access token.
Protected Resource (Person)
- Call this server-to-server API with a valid access token to get the person data.
Access to all server-to-server APIs will be authenticated by MyInfo's API gateway. Prior to calling the APIs, respective consumers are required to have:
- approval of access, onboarding process for the required API resources will be provisioned, and
- authentication credentials are then supplied and exchanged.
Authentication methods provided by MyInfo's API gateway on internet:
- OAuth 2.0 using
RS256digital signature (see "Request Signing" section below) - Digital signature should be produced using a RSA private key with corresponding public certificate issued by one of the following compatible CAs:
- digiCert
- Entrust
- Comodo
- VeriSign
- GlobalSign
- GeoTrust
- Thawte
NOTE: Test and Production Environments only
All server-to-server API requests are to be digitally signed, by including the following parameters and values in the Authorization header:
PKI_SIGN app_id="{app_id}",
nonce="{random_nonce}",
signature_method="RS256",
signature="{base64_url_percent_encoded_signature}",
timestamp="{unix_epoch_in_milliseconds}"Note: Above sample is separated by lines for ease-of-reading, and new-line denotations are to be omitted in the actual request.
{app_id}is the APP ID credential supplied upon onboarding,{random_nonce}is an unique randomly generated text used for replay prevention,{signature_method}is the signature algorithm of the authenticating gateway.- Value of signature_method =
RS256
- Value of signature_method =
{base64_url_percent_encoded_signature}is the binary of the generated signature encoded in Base64 URL-safe format,{unix_epoch_in_milliseconds}is the UNIX epoch time in milliseconds
Sample header with authorization parameters
Below is an example of an Authorization header for the sample application. Make sure you list the parameters in the sequence shown below.
Authorization: PKI_SIGN
app_id="STG2-MYINFO-SELF-TEST",
nonce="150590021034800",
signature_method="RS256",
signature="EEm+HEcNQajb5FkVd82zjojk+daYZXxSGPCOR2GHZeoyjZY1PK+aFMzHfWu7eJZYMa5WaEwWxdOdq5hjNbl8kHD7bMaOks7FgEPdjE++TNomfv7SMktDnIvZmPYAxhjb/C9POU2KT6tSlZT/Si/qMgD1cryaPwSeMoM59UZa1GzYmqlkveba7rma58uGwb3wZFH0n57UnouR6LYXDOOLkqi8uMZBuvRUvSJRXETAj2N0hT+4QJiN96Ct6IEQh/woZh0o74K5Ol9PpDSM08qC7Lj6N/k694J+hbBQVVviGn7/6mDkfbwdMDuoKs4t7NpqmAnwT+xaQSIZcexfrAVQYA==",
timestamp="1505900210349"
Sample Code in NodeJS
// generates the security headers for calling API gateway
function generateAuthorizationHeader(url, params, method, strContentType, authType, appId, keyCertContent, passphrase) {
if (authType == "L2") {
return generateRS256Header(url, params, method, strContentType, appId, keyCertContent, passphrase);
} else {
return "";
}
};
// Signing Your Requests
function generateRS256Header(url, params, method, strContentType, appId, keyCertContent, keyCertPassphrase) {
var nonceValue = nonce();
var timestamp = (new Date).getTime();
// A) Construct the Authorisation Token Parameters
var defaultAuthHeaders = {
"app_id": appId, // App ID assigned to your application
"nonce": nonceValue, // secure random number
"signature_method": "RS256",
"timestamp": timestamp // Unix epoch time
};
// B) Forming the Base String
// Base String is a representation of the entire request (ensures message integrity)
// i) Normalize request parameters
var baseParams = sortJSON(_.merge(defaultAuthHeaders, params));
var baseParamsStr = qs.stringify(baseParams);
baseParamsStr = qs.unescape(baseParamsStr); // url safe
// ii) concatenate request elements (HTTP method + url + base string parameters)
var baseString = method.toUpperCase() + "&" + url + "&" + baseParamsStr;
// C) Signing Base String to get Digital Signature
var signWith = {
key: fs.readFileSync(keyCertContent, 'utf8')
}; // Provides private key
// Load pem file containing the x509 cert & private key & sign the base string with it to produce the Digital Signature
var signature = crypto.createSign('RSA-SHA256')
.update(baseString)
.sign(signWith, 'base64');
// D) Assembling the Authorization Header
var strAuthHeader = "PKI_SIGN app_id=\"" + appId + // Defaults to 1st part of incoming request hostname
"\",timestamp=\"" + timestamp +
"\",nonce=\"" + nonceValue +
"\",signature_method=\"RS256\"" +
",signature=\"" + signature +
"\"";
return strAuthHeader;
};
NOTE: Person APIs only
Access Tokens are in JWT format. This JWT complies to the standard 'JSON Web Token (JWT) Profile for OAuth 2.0 Client Authentication and Authorization Grants' (https://tools.ietf.org/html/rfc7523). You will need to verify the token with our public cert (provided during application onboarding).
Sample Code in NodeJS
// Sample Code for Verifying & Decoding JWS or JWT
function verifyJWS(jws, publicCert) {
// verify token
// ignore notbefore check because it gives errors sometimes if the call is too fast.
try {
var jwspayload = jwt.verify(jws, fs.readFileSync(publicCert, 'utf8'), {
algorithms: ['RS256'],
ignoreNotBefore: true
});
return jwspayload;
}
catch(error) {
throw("Error with verifying and decoding JWS");
}
}
NOTE: Person APIs in Test and Production environments only
The response payload for the Person API (for test and production environments) is first signed, then encrypted:
- Signing is done using JWS (JSON Web Signature) format
- Encryption is done using JWE (JSON Web Encryption) Compact Serialization format
Encryption protects the data at rest while a signed payload means, if necessary, you will be able to pass this signed payload to a 3rd party where they can verify the payload's integrity with our public certificate.
In order to read the payload, you have to perform the following steps in order:
- Decrypt the payload with your application's private key.
- Validate the decrypted payload signature with our public key.
After doing the above steps, your application will be able to extract the payload in JSON format.
STEP 1: Decryption
- Encryption is done using your application's public key that you provided during onboarding. Decryption of the payload should be using the private key of that key-pair.
- Current encryption algorithms used:
- RSA-OAEP (for content key wrapping)
- AES256GCM (for content encrytion)
Sample Code in NodeJS
// Sample Code for decrypting JWE
// Decrypt JWE using private key
function decryptJWE(header, encryptedKey, iv, cipherText, tag, privateKey) {
return new Promise((resolve, reject) => {
var keystore = jose.JWK.createKeyStore();
var data = {
"type": "compact",
"ciphertext": cipherText,
"protected": header,
"encrypted_key": encryptedKey,
"tag": tag,
"iv": iv,
"header": JSON.parse(jose.util.base64url.decode(header).toString())
};
keystore.add(fs.readFileSync(privateKey, 'utf8'), "pem")
.then(function(jweKey) {
// {result} is a jose.JWK.Key
jose.JWE.createDecrypt(jweKey)
.decrypt(data)
.then(function(result) {
resolve(JSON.parse(result.payload.toString()));
})
.catch(function(error) {
reject(error);
});
});
})
.catch (error => {
throw "Error with decrypting JWE";
})
}
STEP 2: Verification of Signature
The decrypted payload is signed according to JWS (JSON Web Signature) format, similar to the access token.
- signature algorithm used is
RS256.
Sample Code in NodeJS
// Sample Code for Verifying & Decoding JWS or JWT
function verifyJWS(jws, publicCert) {
// verify payload
// ignore notbefore check because it gives errors sometimes if the call is too fast.
try {
var jwspayload = jwt.verify(jws, fs.readFileSync(publicCert, 'utf8'), {
algorithms: ['RS256'],
ignoreNotBefore: true
});
return jwspayload;
}
catch(error) {
throw("Error with verifying and decoding JWS");
}
}
MyInfo Person data follows a specific structure that you need to understand to traverse the data effectively. This section will explain the structure in detail.
The diagram below illustrates how the data is represented logically:
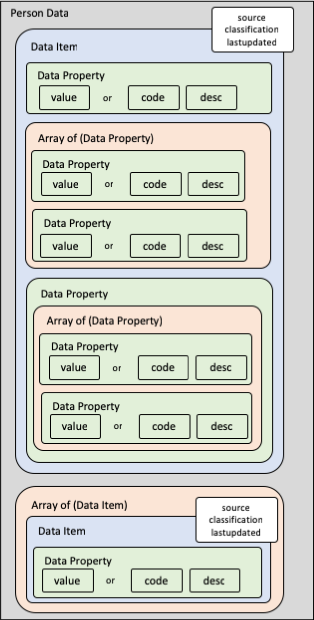
Each top-level data item can either be a data item object or an array of data item objects. Each data item object will consist of the following properties:
classification(Data classification of data field. Default 'C' - Confidential)source(see below)lastupdated(Last updated date of data field. See "full-date" here)unavailable(in certain situations - see below)- additional data properties containing data values or arrays
Data Source
The source property indicates the source of data. Possible values are:
- '1' - Government-verified
- '2' - User provided
- '3' - Field is Not Applicable to Person
- '4' - Verified by SingPass
Note: All Government-verified fields must be non-editable on your digital service form (some exceptions apply - see individual field descriptions).
In each data item, there can be multiple data properties or arrays of data properties.
Each data property will contain either:
- a
valueproperty, or - a pair of
codeanddescproperties, or - an array of data properties, or
- other data properties
Note:
valueproperty can be strings, numbers, or dates.codeanddescpairs will contain the code and its matching description.valueis mutually exclusive from (code+desc); i.e. if there is avalue, there will not be anycodeordesc.- Where there is
code, there will always be adesc- novaluewill be present.
Exceptions: For these cases, the values will be directly in the property and not in a value, code or desc subproperty:
- for data item metadata properties; e.g.
classification,source,lastupdated, andunavailable - for discriminator properties; e.g.
typein address formats
Sometimes, a requested data item is not applicable to the person. Examples include:
- a foreigner will never have a
regadddata item. - a singapore citizen or permanent resident will never have
passtypedata item.
For a full list, refer to the "Data Catalog" section of MyInfo API Data in our portal.
Note: When a requested data item is not applicable to the person, the source property will be 3. In such cases, please ignore the data item completely.
Data Item Not Applicable
When a requested data item is not applicable to the entity:
- for data item objects, the
sourceproperty will be 3 - for data item arrays, an empty array will be returned
In such cases, please ignore the data item completely.
Data Property Not Applicable
- When a data property is not applicable to the person, it will not appear in the schema of that particular entity type.
- Please check the Person schema to identify which data properties are not applicable to the person type.
The RESTful APIs used HTTP specification standard status codes to indicate the success or failure of each request. Except gateway errors, the response content will be in the following JSON format:
{
"code": "integer (int32)",
"message": "string"
}Refer to the individual API definitions for the error codes you might encounter for each API.
Please refer to the NDI {api} Portal for the following supporting materials where relevant:
- MyInfo demo app
- Code reference tables
- Test accounts for test environments
- Reference user journey templates
For technical queries, contact support@myinfo.gov.sg.
For business queries, contact partner@myinfo.gov.sg.
PKISign
PKI digital signature for server to server calls. See Request Signing for more details.
| Security scheme type: | HTTP |
|---|---|
| HTTP Authorization Scheme | Mutual authentication via PKI digital signature in Authorization header |
OAuth2
The following are the available OAuth2 scopes for MyInfo APIs
| Security scheme type: | OAuth2 |
|---|---|
| authorizationCode OAuth Flow | Authorization URL: /com/v3/authorise Token URL: /com/v3/token Scopes:
|
Person-Sample
Retrieves a sample Person data from MyInfo based on UIN/FIN.
This API does not use OAuth2.0 to perform authentication or authorisation, and does not require authorisation token and digital signature.
Note: Null value indicates that an attribute is unavailable.
path Parameters
| uinfin required | string Example: "S9812381D" |
query Parameters
| attributes | Array of string Example: "name,hanyupinyinname" Comma separated list of attributes requested. Possible attributes are listed in the scopes of the OAuth2 Security Schema above. |
Responses
OK.
Note:
- Response will be a JSON object.
Request samples
- Shell
curl https://sandbox.api.myinfo.gov.sg/com/v3/person-sample/S9812381DResponse samples
- 200
- "uinfin": {
- "value": "S1111111D",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "partialuinfin": {
- "value": "*****111D",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "name": {
- "value": "TAN XIAO HUI",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "hanyupinyinname": {
- "value": "CHEN XIAO HUI",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "aliasname": {
- "value": "TRICIA TAN XIAO HUI",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "hanyupinyinaliasname": {
- "value": "TRICIA CHEN XIAO HUI",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "marriedname": {
- "value": "",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "sex": {
- "code": "F",
- "desc": "FEMALE",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "race": {
- "code": "CN",
- "desc": "CHINESE",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "secondaryrace": {
- "code": "EU",
- "desc": "EURASIAN",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "dialect": {
- "code": "SG",
- "desc": "SWISS GERMAN",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "nationality": {
- "code": "SG",
- "desc": "SINGAPORE CITIZEN",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "dob": {
- "value": "1958-05-17",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "birthcountry": {
- "code": "SG",
- "desc": "SINGAPORE",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "residentialstatus": {
- "code": "C",
- "desc": "CITIZEN",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "passportnumber": {
- "value": "E35463874W",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "passportexpirydate": {
- "value": "2020-01-01",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "regadd": {
- "type": "SG",
- "block": {
- "value": "548"
- "building": {
- "value": ""
- "floor": {
- "value": "09"
- "unit": {
- "value": "128"
- "street": {
- "value": "BEDOK NORTH AVENUE 1"
- "postal": {
- "value": "460548"
- "country": {
- "code": "SG",
- "desc": "SINGAPORE"
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "mailadd": {
- "type": "SG",
- "block": {
- "value": "548"
- "building": {
- "value": ""
- "floor": {
- "value": "09"
- "unit": {
- "value": "128"
- "street": {
- "value": "BEDOK NORTH AVENUE 1"
- "postal": {
- "value": "460548"
- "country": {
- "code": "SG",
- "desc": "SINGAPORE"
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "billadd": {
- "type": "SG",
- "block": {
- "value": "548"
- "building": {
- "value": ""
- "floor": {
- "value": "09"
- "unit": {
- "value": "128"
- "street": {
- "value": "BEDOK NORTH AVENUE 1"
- "postal": {
- "value": "460548"
- "country": {
- "code": "SG",
- "desc": "SINGAPORE"
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "housingtype": {
- "code": "123",
- "desc": "TERRACE HOUSE",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "hdbtype": {
- "code": "112",
- "desc": "2-ROOM FLAT (HDB)",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "hdbownership": [
- {
- "noofowners": {
- "value": 2
- "address": {
- "type": "SG",
- "block": {
- "value": "548"
- "building": {
- "value": ""
- "floor": {
- "value": "09"
- "unit": {
- "value": "128"
- "street": {
- "value": "BEDOK NORTH AVENUE 1"
- "postal": {
- "value": "460548"
- "country": {
- "code": "SG",
- "desc": "SINGAPORE"
- "hdbtype": {
- "code": "112",
- "desc": "2-ROOM FLAT (HDB)"
- "leasecommencementdate": {
- "value": "2008-06-13"
- "termoflease": {
- "value": 99
- "dateofpurchase": {
- "value": "2008-06-13"
- "dateofownershiptransfer": {
- "value": "2018-06-13"
- "loangranted": {
- "value": 310000.01
- "originalloanrepayment": {
- "value": 25
- "balanceloanrepayment": {
- "years": {
- "value": 2
- "months": {
- "value": 6
- "outstandingloanbalance": {
- "value": 50000.01
- "monthlyloaninstalment": {
- "value": 1000.01
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "ownerprivate": {
- "value": false,
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "email": {
- "value": "test@gmail.com",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "homeno": {
- "prefix": {
- "value": "+"
- "areacode": {
- "value": "65"
- "nbr": {
- "value": "66132665"
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "mobileno": {
- "prefix": {
- "value": "+"
- "areacode": {
- "value": "65"
- "nbr": {
- "value": "66132665"
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "marital": {
- "code": "2",
- "desc": "MARRIED",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "marriagecertno": {
- "value": "123456789012345",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "countryofmarriage": {
- "code": "SG",
- "desc": "SINGAPORE",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "marriagedate": {
- "value": "2007-01-01",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "divorcedate": {
- "value": "",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "childrenbirthrecords": [
- {
- "birthcertno": {
- "value": "S5562882C"
- "name": {
- "value": "Jo Tan Pei Ni"
- "hanyupinyinname": {
- "value": "Cheng Pei Ni"
- "aliasname": {
- "value": ""
- "hanyupinyinaliasname": {
- "value": ""
- "marriedname": {
- "value": ""
- "sex": {
- "code": "F",
- "desc": "FEMALE"
- "race": {
- "code": "CN",
- "desc": "CHINESE"
- "secondaryrace": {
- "code": "",
- "desc": ""
- "dialect": {
- "code": "HK",
- "desc": "HOKKIEN"
- "lifestatus": {
- "code": "D",
- "desc": "DECEASED"
- "dob": {
- "value": "2011-09-10"
- "tob": {
- "value": "0901"
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "sponsoredchildrenrecords": [
- {
- "nric": {
- "value": "S5562882C"
- "name": {
- "value": "Jo Tan Pei Ni"
- "hanyupinyinname": {
- "value": "Cheng Pei Ni"
- "aliasname": {
- "value": ""
- "hanyupinyinaliasname": {
- "value": ""
- "marriedname": {
- "value": ""
- "sex": {
- "code": "F",
- "desc": "FEMALE"
- "race": {
- "code": "CN",
- "desc": "CHINESE"
- "secondaryrace": {
- "code": "",
- "desc": ""
- "dialect": {
- "code": "HK",
- "desc": "HOKKIEN"
- "dob": {
- "value": "2011-09-10"
- "birthcountry": {
- "code": "SG",
- "desc": "SINGAPORE"
- "lifestatus": {
- "code": "A",
- "desc": "ALIVE"
- "residentialstatus": {
- "code": "C",
- "desc": "Citizen"
- "nationality": {
- "code": "SG",
- "desc": "SINGAPORE CITIZEN"
- "scprgrantdate": {
- "value": "2015-06-13"
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "edulevel": {
- "code": "7",
- "desc": "BACHELOR'S OR EQUIVALENT",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "gradyear": {
- "value": "2006",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "schoolname": {
- "code": "T07GS3011J",
- "desc": "SIGLAP SECONDARY SCHOOL",
- "value": "",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "occupation": {
- "code": "53201",
- "desc": "HEALTHCARE ASSISTANT",
- "value": "",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "employment": {
- "value": "ALPHA",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "passtype": {
- "code": "RPass",
- "desc": "Work Permit",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "passstatus": {
- "value": "Live",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "passexpirydate": {
- "value": "2022-12-31",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "employmentsector": {
- "value": "Manufacturing",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "householdincome": {
- "high": {
- "value": 5999
- "low": {
- "value": 5000
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "noa-basic": {
- "amount": {
- "value": 100000.01
- "yearofassessment": {
- "value": "2018"
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "noa": {
- "amount": {
- "value": 100000.01
- "yearofassessment": {
- "value": "2018"
- "employment": {
- "value": 100000.01
- "trade": {
- "value": 0
- "rent": {
- "value": 0
- "interest": {
- "value": 0
- "taxclearance": {
- "value": "N"
- "category": {
- "value": "ORIGINAL"
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "noahistory-basic": {
- "noas": [
- {
- "amount": {
- "value": 100000.01
- "yearofassessment": {
- "value": "2018"
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "noahistory": {
- "noas": [
- {
- "amount": {
- "value": 100000.01
- "yearofassessment": {
- "value": "2018"
- "employment": {
- "value": 100000.01
- "trade": {
- "value": 0
- "rent": {
- "value": 0
- "interest": {
- "value": 0
- "taxclearance": {
- "value": "N"
- "category": {
- "value": "ORIGINAL"
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "cpfcontributions": {
- "history": [
- {
- "date": {
- "value": "2016-12-01"
- "amount": {
- "value": 500
- "month": {
- "value": "2016-11"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2016-12-12"
- "amount": {
- "value": 500
- "month": {
- "value": "2016-12"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2016-12-21"
- "amount": {
- "value": 500
- "month": {
- "value": "2016-12"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-01-01"
- "amount": {
- "value": 500
- "month": {
- "value": "2016-12"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-01-12"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-01"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-01-21"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-01"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-02-01"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-01"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-02-12"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-02"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-02-21"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-02"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-03-01"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-02"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-03-12"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-03"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-03-21"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-03"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-04-01"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-03"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-04-12"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-04"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-04-21"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-04"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-05-01"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-04"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-05-12"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-05"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-05-21"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-05"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-06-01"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-05"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-06-12"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-06"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-06-21"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-06"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-07-01"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-06"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-07-12"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-07"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-07-21"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-07"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-08-01"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-07"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-08-12"
- "amount": {
- "value": 750
- "month": {
- "value": "2017-08"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "date": {
- "value": "2017-08-21"
- "amount": {
- "value": 750
- "month": {
- "value": "2017-08"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "date": {
- "value": "2017-09-01"
- "amount": {
- "value": 750
- "month": {
- "value": "2017-08"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "date": {
- "value": "2017-09-12"
- "amount": {
- "value": 750
- "month": {
- "value": "2017-09"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "date": {
- "value": "2017-09-21"
- "amount": {
- "value": 750
- "month": {
- "value": "2017-09"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "date": {
- "value": "2017-10-01"
- "amount": {
- "value": 750
- "month": {
- "value": "2017-09"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "date": {
- "value": "2017-10-12"
- "amount": {
- "value": 750
- "month": {
- "value": "2017-10"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "date": {
- "value": "2017-10-21"
- "amount": {
- "value": 750
- "month": {
- "value": "2017-10"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "date": {
- "value": "2017-11-01"
- "amount": {
- "value": 750
- "month": {
- "value": "2017-10"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "date": {
- "value": "2017-11-12"
- "amount": {
- "value": 750
- "month": {
- "value": "2017-11"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "date": {
- "value": "2017-11-21"
- "amount": {
- "value": 750
- "month": {
- "value": "2017-11"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "date": {
- "value": "2017-12-01"
- "amount": {
- "value": 750
- "month": {
- "value": "2017-11"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "date": {
- "value": "2017-12-12"
- "amount": {
- "value": 750
- "month": {
- "value": "2017-12"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "date": {
- "value": "2017-12-21"
- "amount": {
- "value": 750
- "month": {
- "value": "2017-12"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "date": {
- "value": "2018-01-01"
- "amount": {
- "value": 750
- "month": {
- "value": "2017-12"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "date": {
- "value": "2018-01-12"
- "amount": {
- "value": 750
- "month": {
- "value": "2018-01"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "date": {
- "value": "2018-01-21"
- "amount": {
- "value": 750
- "month": {
- "value": "2018-01"
- "employer": {
- "value": "Delta Marine Consultants PL"
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "cpfemployers": {
- "history": [
- {
- "month": {
- "value": "2016-11"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2016-12"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2016-12"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2016-12"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-01"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-01"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-01"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-02"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-02"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-02"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-03"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-03"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-03"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-04"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-04"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-04"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-05"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-05"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-05"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-06"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-06"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-06"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-07"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-07"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-07"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-08"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "month": {
- "value": "2017-08"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "month": {
- "value": "2017-08"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "month": {
- "value": "2017-09"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "month": {
- "value": "2017-09"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "month": {
- "value": "2017-09"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "month": {
- "value": "2017-10"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "month": {
- "value": "2017-10"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "month": {
- "value": "2017-10"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "month": {
- "value": "2017-11"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "month": {
- "value": "2017-11"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "month": {
- "value": "2017-11"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "month": {
- "value": "2017-12"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "month": {
- "value": "2017-12"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "month": {
- "value": "2017-12"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "month": {
- "value": "2018-01"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "month": {
- "value": "2018-01"
- "employer": {
- "value": "Delta Marine Consultants PL"
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "cpfbalances": {
- "ma": {
- "value": 11470.71
- "oa": {
- "value": 1581.48
- "sa": {
- "value": 21967.09
- "ra": {
- "value": 0.01
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "vehicles": [
- {
- "vehicleno": {
- "value": "SDF1235A"
- "type": {
- "value": "PASSENGER MOTOR CAR"
- "iulabelno": {
- "value": ""
- "make": {
- "value": "TOYOTA"
- "model": {
- "value": "COROLLA ALTIS"
- "chassisno": {
- "value": "ZC11S1735800"
- "engineno": {
- "value": "M13A1837453"
- "motorno": {
- "value": ""
- "yearofmanufacture": {
- "value": "2010"
- "firstregistrationdate": {
- "value": "2010-06-06"
- "originalregistrationdate": {
- "value": "2010-06-06"
- "coecategory": {
- "value": "A - CAR UP TO 1600CC & 97KW (130BHP)"
- "coeexpirydate": {
- "value": "2020-06-05"
- "roadtaxexpirydate": {
- "value": "2020-06-05"
- "quotapremium": {
- "value": 14000.01
- "openmarketvalue": {
- "value": 25000.01
- "co2emission": {
- "value": 146.01
- "status": {
- "code": "1",
- "desc": "LIVE"
- "primarycolour": {
- "value": "BLACK"
- "secondarycolour": {
- "value": "WHITE"
- "attachment1": {
- "value": "DISABLED"
- "attachment2": {
- "value": "WITH SUN ROOF"
- "attachment3": {
- "value": "SIDE CURTAIN"
- "scheme": {
- "value": "REVISED OFF-PEAK CAR"
- "thcemission": {
- "value": 1.011001
- "coemission": {
- "value": 1.100001
- "noxemission": {
- "value": 0.011001
- "pmemission": {
- "value": 0.007
- "enginecapacity": {
- "value": 1600
- "powerrate": {
- "value": 1.41
- "effectiveownership": {
- "value": "2010-08-31T20:12:12+08:00"
- "propellant": {
- "value": "Compressed Natural Gas"
- "maximumunladenweight": {
- "value": 1500
- "maximumladenweight": {
- "value": 1795
- "minimumparfbenefit": {
- "value": 8770.01
- "nooftransfers": {
- "value": 2
- "vpc": {
- "value": "1234567890"
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "drivinglicence": {
- "comstatus": {
- "code": "Y",
- "desc": "ELIGIBLE"
- "totaldemeritpoints": {
- "value": 0
- "suspension": {
- "startdate": {
- "value": ""
- "enddate": {
- "value": ""
- "disqualification": {
- "startdate": {
- "value": ""
- "enddate": {
- "value": ""
- "revocation": {
- "startdate": {
- "value": ""
- "enddate": {
- "value": ""
- "pdl": {
- "validity": {
- "code": "V",
- "desc": "VALID"
- "expirydate": {
- "value": "2020-06-15"
- "classes": [
- {
- "class": {
- "value": "2A"
- {
- "class": {
- "value": "3A"
- "qdl": {
- "validity": {
- "code": "V",
- "desc": "VALID"
- "expirydate": {
- "value": "2020-06-15"
- "classes": [
- {
- "class": {
- "value": "2A"
- "issuedate": {
- "value": "2018-06-06"
- {
- "class": {
- "value": "3A"
- "issuedate": {
- "value": "2018-06-06"
- "photocardserialno": {
- "value": "115616"
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
Token
This API generates an access token when presented with a valid authcode obtained from the Authorise API. This token can then be used to request for the user's data that were consented.
Authorizations:
header Parameters
| Authorization required | string Add authorization token constructed containing the RSA digital signature of the base string. Refer to https://api.singpass.gov.sg/library/myinfo/developers/tutorial3 on how this token should be generated. Note: This header is not required when calling Sandbox API. |
Request Body schema: application/x-www-form-urlencoded
| code required | string The authcode given by the authorise API. |
| grant_type | string Default: "authorization_code" Grant type for getting token (default "authorization_code") |
| client_secret required | string Secret key given to your application during onboarding. |
| client_id required | string Unique ID for your application. |
| redirect_uri required | string Application's callback URL. |
| state | string Identifier that represents the user's session with the client, provided earlier during the authorise API call. |
Responses
OK.
Returning a JSON object which contains the authorization access token (JWT) that will be used to retrieve the data from MyInfo.
Possible scenarios:
- Same authcode in the body is being re-used. We do not allow same authcode being used in multiple calls. Ensure that authcode is not repeated.
- AuthCode error - missing, invalid, expired, revoked
Unauthorized.
Possible scenarios:
- No security header given (HTTP 'Authorization' header)
- Invalid App ID used. Digital service is not registered with MyInfo
- The timestamp of server is not synchronised. Check timestamp of server.
- The value of the nonce in the authorisation header was deemed to be repeated. Check that the nonce is not re-used
- Ensure HTTP 'Authorization' header to be 'PKI_SIGN'
- Signature incorrect - Verify your signature by using our signature verifier tool and ensure correct key is used to sign the base string.
- Ensure that base string contains all parameters required
- Ensure attributes in base string are separate by comma(,), and not %2C
- Ensure that correct key is used to sign the base string
- Ensure that HTTP call is made with the same query/body parameters used to formulate the base string.
- Ensure the base string contains the following:
- HTTP GET method(in uppercase)
- API (e.g. https://..)
- These parameters:
- app_id
- nonce
- signature
- signature_method
- timestamp
Forbidden
Possible scenarios:
- Incorrect API URL used. Refer to tutorial for the correct API URL(test/production)
Unexpected error. Check response body for actual error.
Request samples
- NodeJS
// function to prepare request for TOKEN API function createTokenRequest(code) { var cacheCtl = "no-cache"; var contentType = "application/x-www-form-urlencoded"; var method = "POST"; var request = null; // preparing the request with header and parameters // assemble params for Token API var strParams = "grant_type=authorization_code" + "&code=" + code + "&redirect_uri=" + _redirectUrl + "&client_id=" + _clientId + "&client_secret=" + _clientSecret; var params = querystring.parse(strParams); // assemble headers for Token API var strHeaders = "Content-Type=" + contentType + "&Cache-Control=" + cacheCtl; var headers = querystring.parse(strHeaders); // Sign request and add Authorization Headers var authHeaders = generateAuthorizationHeader( _tokenApiUrl, params, method, contentType, _authLevel, _clientId, _privateKeyContent, _clientSecret ); if (!_.isEmpty(authHeaders)) { _.set(headers, "Authorization", authHeaders); } var request = restClient.post(_tokenApiUrl); // Set headers if (!_.isUndefined(headers) && !_.isEmpty(headers)) request.set(headers); // Set Params if (!_.isUndefined(params) && !_.isEmpty(params)) request.send(params); return request; }
Response samples
- 200
- 400
- 401
- 403
- 500
- "token_type": "Bearer",
- "id_token": "string",
- "access_token": {
- "tokenName": "access_token",
- "sub": "string",
- "scope": [
- "string"
- "nbf": "string",
- "iss": "string",
- "expires_in": "string",
- "iat": "string",
- "exp": "string",
- "realm": "string",
- "aud": "string",
- "jti": "string",
- "token_type": "Bearer",
- "authGrantId": "string",
- "auditTrackingId": "string"
Person
This API returns user's data from MyInfo when presented with a valid access token obtained from the Token API.
Note: Null value indicates that an attribute is unavailable.
path Parameters
| uinfin required | string Example: "S9812381D" UIN/FIN of user |
query Parameters
| txnNo | string Transaction ID from requesting digital services for cross referencing. |
| attributes required | Array of string Example: "name,hanyupinyinname" Comma separated list of attributes requested. Possible attributes are listed in the scopes of the OAuth2 Security Schema above. |
| client_id required | string Example: "STG-180099999K-TEST01" Unique ID for your application. |
| subentity | string <= 10 characters Example: "PARTNER001" Field that allows traceability to platform's client who will be receiving the person data. Only applicable to |
header Parameters
| Authorization required | any Add authorization token constructed containing the RSA digital signature of the base string. Refer to https://api.singpass.gov.sg/library/myinfo/developers/tutorial3 on how this token should be generated. Also include the access token (JWT) from /token API in your header prefixed with 'Bearer'. Note: Only the Bearer token is required when calling Sandbox API. |
Responses
OK.
Note:
- Response Content-Type will be 'application/jose', which is a JSON object conforming to the JWE standard (https://tools.ietf.org/html/rfc7516).
- Response contents are first signed, then encrypted. In order to access the data, your application should do the following steps in order:
- Decrypt the payload with your application's private key.
- Validate the decrypted payload signature with our public key.
- After doing the above steps, your application will be able to extract the payload in JSON format.
Unauthorized.
Possible scenarios:
- No security header given (HTTP 'Authorization' header)
- Invalid App ID used. Digital service is not registered with MyInfo
- The timestamp of server is not synchronised. Check timestamp of server.
- The value of the nonce in the authorisation header was deemed to be repeated. Check that the nonce is not re-used
- Ensure HTTP 'Authorization' header to be 'PKI_SIGN'
- Signature incorrect - Verify your signature by using our signature verifier tool and ensure correct key is used to sign the base string.
- Ensure that base string contains all parameters required
- Ensure attributes in base string are separate by comma(,), and not %2C
- Ensure that correct key is used to sign the base string
- Ensure that HTTP call is made with the same query/body parameters used to formulate the base string.
- Ensure the base string contains the following:
- HTTP GET method(in uppercase)
- API (e.g. https://..)
- These parameters:
- app_id
- nonce
- signature
- signature_method
- timestamp
- The requested UIN/FIN does not match the UIN/FIN of the person who logged in
- Requested attributes do not match the attributes consented by person. This happens if the list of attributes in your request are different from the attributes specified when calling the token API.
Details will be given in the error object returned.
Forbidden
Possible scenarios:
- Incorrect API URL used. Refer to tutorial for the correct API URL(test/production)
- Digital service is not registered with MyInfo.
- Request contains attributes not allowable for the digital service.
Not Found.
Possible scenarios.
- Missing MyInfo profile due to UIN/FIN accessing his MyInfo account less than a day after SingPass account activation.
Unexpected error. Check response body for actual error.
Request samples
- NodeJS
// function to prepare request for PERSON API function createPersonRequest(uinfin, validToken) { var url = _personApiUrl + "/" + uinfin + "/"; var cacheCtl = "no-cache"; var method = "GET"; var request = null; // assemble params for Person API var strParams = "client_id=" + _clientId + "&attributes=" + _attributes; var params = querystring.parse(strParams); // assemble headers for Person API var strHeaders = "Cache-Control=" + cacheCtl; var headers = querystring.parse(strHeaders); var authHeaders; // Sign request and add Authorization Headers authHeaders = generateAuthorizationHeader( url, params, method, "", // no content type needed for GET _authLevel, _clientId, _privateKeyContent, _clientSecret ); if (!_.isEmpty(authHeaders)) { _.set(headers, "Authorization", authHeaders + ",Bearer " + validToken); } else { // NOTE: include access token in Authorization header as "Bearer " (with space behind) _.set(headers, "Authorization", "Bearer " + validToken); } // invoke token API var request = restClient.get(url); // Set headers if (!_.isUndefined(headers) && !_.isEmpty(headers)) request.set(headers); // Set Params if (!_.isUndefined(params) && !_.isEmpty(params)) request.query(params); return request; }
Response samples
- 200
- 401
- 403
- 404
- 500
- "uinfin": {
- "value": "S1111111D",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "partialuinfin": {
- "value": "*****111D",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "name": {
- "value": "TAN XIAO HUI",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "hanyupinyinname": {
- "value": "CHEN XIAO HUI",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "aliasname": {
- "value": "TRICIA TAN XIAO HUI",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "hanyupinyinaliasname": {
- "value": "TRICIA CHEN XIAO HUI",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "marriedname": {
- "value": "",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "sex": {
- "code": "F",
- "desc": "FEMALE",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "race": {
- "code": "CN",
- "desc": "CHINESE",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "secondaryrace": {
- "code": "EU",
- "desc": "EURASIAN",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "dialect": {
- "code": "SG",
- "desc": "SWISS GERMAN",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "nationality": {
- "code": "SG",
- "desc": "SINGAPORE CITIZEN",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "dob": {
- "value": "1958-05-17",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "birthcountry": {
- "code": "SG",
- "desc": "SINGAPORE",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "residentialstatus": {
- "code": "C",
- "desc": "CITIZEN",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "passportnumber": {
- "value": "E35463874W",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "passportexpirydate": {
- "value": "2020-01-01",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "regadd": {
- "type": "SG",
- "block": {
- "value": "548"
- "building": {
- "value": ""
- "floor": {
- "value": "09"
- "unit": {
- "value": "128"
- "street": {
- "value": "BEDOK NORTH AVENUE 1"
- "postal": {
- "value": "460548"
- "country": {
- "code": "SG",
- "desc": "SINGAPORE"
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "mailadd": {
- "type": "SG",
- "block": {
- "value": "548"
- "building": {
- "value": ""
- "floor": {
- "value": "09"
- "unit": {
- "value": "128"
- "street": {
- "value": "BEDOK NORTH AVENUE 1"
- "postal": {
- "value": "460548"
- "country": {
- "code": "SG",
- "desc": "SINGAPORE"
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "billadd": {
- "type": "SG",
- "block": {
- "value": "548"
- "building": {
- "value": ""
- "floor": {
- "value": "09"
- "unit": {
- "value": "128"
- "street": {
- "value": "BEDOK NORTH AVENUE 1"
- "postal": {
- "value": "460548"
- "country": {
- "code": "SG",
- "desc": "SINGAPORE"
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "housingtype": {
- "code": "123",
- "desc": "TERRACE HOUSE",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "hdbtype": {
- "code": "112",
- "desc": "2-ROOM FLAT (HDB)",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "hdbownership": [
- {
- "noofowners": {
- "value": 2
- "address": {
- "type": "SG",
- "block": {
- "value": "548"
- "building": {
- "value": ""
- "floor": {
- "value": "09"
- "unit": {
- "value": "128"
- "street": {
- "value": "BEDOK NORTH AVENUE 1"
- "postal": {
- "value": "460548"
- "country": {
- "code": "SG",
- "desc": "SINGAPORE"
- "hdbtype": {
- "code": "112",
- "desc": "2-ROOM FLAT (HDB)"
- "leasecommencementdate": {
- "value": "2008-06-13"
- "termoflease": {
- "value": 99
- "dateofpurchase": {
- "value": "2008-06-13"
- "dateofownershiptransfer": {
- "value": "2018-06-13"
- "loangranted": {
- "value": 310000.01
- "originalloanrepayment": {
- "value": 25
- "balanceloanrepayment": {
- "years": {
- "value": 2
- "months": {
- "value": 6
- "outstandingloanbalance": {
- "value": 50000.01
- "monthlyloaninstalment": {
- "value": 1000.01
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "ownerprivate": {
- "value": false,
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "email": {
- "value": "test@gmail.com",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "homeno": {
- "prefix": {
- "value": "+"
- "areacode": {
- "value": "65"
- "nbr": {
- "value": "66132665"
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "mobileno": {
- "prefix": {
- "value": "+"
- "areacode": {
- "value": "65"
- "nbr": {
- "value": "66132665"
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "marital": {
- "code": "2",
- "desc": "MARRIED",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "marriagecertno": {
- "value": "123456789012345",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "countryofmarriage": {
- "code": "SG",
- "desc": "SINGAPORE",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "marriagedate": {
- "value": "2007-01-01",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "divorcedate": {
- "value": "",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "childrenbirthrecords": [
- {
- "birthcertno": {
- "value": "S5562882C"
- "name": {
- "value": "Jo Tan Pei Ni"
- "hanyupinyinname": {
- "value": "Cheng Pei Ni"
- "aliasname": {
- "value": ""
- "hanyupinyinaliasname": {
- "value": ""
- "marriedname": {
- "value": ""
- "sex": {
- "code": "F",
- "desc": "FEMALE"
- "race": {
- "code": "CN",
- "desc": "CHINESE"
- "secondaryrace": {
- "code": "",
- "desc": ""
- "dialect": {
- "code": "HK",
- "desc": "HOKKIEN"
- "lifestatus": {
- "code": "D",
- "desc": "DECEASED"
- "dob": {
- "value": "2011-09-10"
- "tob": {
- "value": "0901"
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "sponsoredchildrenrecords": [
- {
- "nric": {
- "value": "S5562882C"
- "name": {
- "value": "Jo Tan Pei Ni"
- "hanyupinyinname": {
- "value": "Cheng Pei Ni"
- "aliasname": {
- "value": ""
- "hanyupinyinaliasname": {
- "value": ""
- "marriedname": {
- "value": ""
- "sex": {
- "code": "F",
- "desc": "FEMALE"
- "race": {
- "code": "CN",
- "desc": "CHINESE"
- "secondaryrace": {
- "code": "",
- "desc": ""
- "dialect": {
- "code": "HK",
- "desc": "HOKKIEN"
- "dob": {
- "value": "2011-09-10"
- "birthcountry": {
- "code": "SG",
- "desc": "SINGAPORE"
- "lifestatus": {
- "code": "A",
- "desc": "ALIVE"
- "residentialstatus": {
- "code": "C",
- "desc": "Citizen"
- "nationality": {
- "code": "SG",
- "desc": "SINGAPORE CITIZEN"
- "scprgrantdate": {
- "value": "2015-06-13"
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "edulevel": {
- "code": "7",
- "desc": "BACHELOR'S OR EQUIVALENT",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "gradyear": {
- "value": "2006",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "schoolname": {
- "code": "T07GS3011J",
- "desc": "SIGLAP SECONDARY SCHOOL",
- "value": "",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "occupation": {
- "code": "53201",
- "desc": "HEALTHCARE ASSISTANT",
- "value": "",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "employment": {
- "value": "ALPHA",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "passtype": {
- "code": "RPass",
- "desc": "Work Permit",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "passstatus": {
- "value": "Live",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "passexpirydate": {
- "value": "2022-12-31",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "employmentsector": {
- "value": "Manufacturing",
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "householdincome": {
- "high": {
- "value": 5999
- "low": {
- "value": 5000
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "noa-basic": {
- "amount": {
- "value": 100000.01
- "yearofassessment": {
- "value": "2018"
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "noa": {
- "amount": {
- "value": 100000.01
- "yearofassessment": {
- "value": "2018"
- "employment": {
- "value": 100000.01
- "trade": {
- "value": 0
- "rent": {
- "value": 0
- "interest": {
- "value": 0
- "taxclearance": {
- "value": "N"
- "category": {
- "value": "ORIGINAL"
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "noahistory-basic": {
- "noas": [
- {
- "amount": {
- "value": 100000.01
- "yearofassessment": {
- "value": "2018"
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "noahistory": {
- "noas": [
- {
- "amount": {
- "value": 100000.01
- "yearofassessment": {
- "value": "2018"
- "employment": {
- "value": 100000.01
- "trade": {
- "value": 0
- "rent": {
- "value": 0
- "interest": {
- "value": 0
- "taxclearance": {
- "value": "N"
- "category": {
- "value": "ORIGINAL"
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "cpfcontributions": {
- "history": [
- {
- "date": {
- "value": "2016-12-01"
- "amount": {
- "value": 500
- "month": {
- "value": "2016-11"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2016-12-12"
- "amount": {
- "value": 500
- "month": {
- "value": "2016-12"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2016-12-21"
- "amount": {
- "value": 500
- "month": {
- "value": "2016-12"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-01-01"
- "amount": {
- "value": 500
- "month": {
- "value": "2016-12"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-01-12"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-01"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-01-21"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-01"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-02-01"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-01"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-02-12"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-02"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-02-21"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-02"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-03-01"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-02"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-03-12"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-03"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-03-21"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-03"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-04-01"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-03"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-04-12"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-04"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-04-21"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-04"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-05-01"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-04"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-05-12"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-05"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-05-21"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-05"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-06-01"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-05"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-06-12"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-06"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-06-21"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-06"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-07-01"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-06"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-07-12"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-07"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-07-21"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-07"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-08-01"
- "amount": {
- "value": 500
- "month": {
- "value": "2017-07"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "date": {
- "value": "2017-08-12"
- "amount": {
- "value": 750
- "month": {
- "value": "2017-08"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "date": {
- "value": "2017-08-21"
- "amount": {
- "value": 750
- "month": {
- "value": "2017-08"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "date": {
- "value": "2017-09-01"
- "amount": {
- "value": 750
- "month": {
- "value": "2017-08"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "date": {
- "value": "2017-09-12"
- "amount": {
- "value": 750
- "month": {
- "value": "2017-09"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "date": {
- "value": "2017-09-21"
- "amount": {
- "value": 750
- "month": {
- "value": "2017-09"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "date": {
- "value": "2017-10-01"
- "amount": {
- "value": 750
- "month": {
- "value": "2017-09"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "date": {
- "value": "2017-10-12"
- "amount": {
- "value": 750
- "month": {
- "value": "2017-10"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "date": {
- "value": "2017-10-21"
- "amount": {
- "value": 750
- "month": {
- "value": "2017-10"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "date": {
- "value": "2017-11-01"
- "amount": {
- "value": 750
- "month": {
- "value": "2017-10"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "date": {
- "value": "2017-11-12"
- "amount": {
- "value": 750
- "month": {
- "value": "2017-11"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "date": {
- "value": "2017-11-21"
- "amount": {
- "value": 750
- "month": {
- "value": "2017-11"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "date": {
- "value": "2017-12-01"
- "amount": {
- "value": 750
- "month": {
- "value": "2017-11"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "date": {
- "value": "2017-12-12"
- "amount": {
- "value": 750
- "month": {
- "value": "2017-12"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "date": {
- "value": "2017-12-21"
- "amount": {
- "value": 750
- "month": {
- "value": "2017-12"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "date": {
- "value": "2018-01-01"
- "amount": {
- "value": 750
- "month": {
- "value": "2017-12"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "date": {
- "value": "2018-01-12"
- "amount": {
- "value": 750
- "month": {
- "value": "2018-01"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "date": {
- "value": "2018-01-21"
- "amount": {
- "value": 750
- "month": {
- "value": "2018-01"
- "employer": {
- "value": "Delta Marine Consultants PL"
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "cpfemployers": {
- "history": [
- {
- "month": {
- "value": "2016-11"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2016-12"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2016-12"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2016-12"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-01"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-01"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-01"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-02"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-02"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-02"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-03"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-03"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-03"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-04"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-04"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-04"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-05"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-05"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-05"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-06"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-06"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-06"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-07"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-07"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-07"
- "employer": {
- "value": "Crystal Horse Invest Pte Ltd"
- {
- "month": {
- "value": "2017-08"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "month": {
- "value": "2017-08"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "month": {
- "value": "2017-08"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "month": {
- "value": "2017-09"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "month": {
- "value": "2017-09"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "month": {
- "value": "2017-09"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "month": {
- "value": "2017-10"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "month": {
- "value": "2017-10"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "month": {
- "value": "2017-10"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "month": {
- "value": "2017-11"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "month": {
- "value": "2017-11"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "month": {
- "value": "2017-11"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "month": {
- "value": "2017-12"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "month": {
- "value": "2017-12"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "month": {
- "value": "2017-12"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "month": {
- "value": "2018-01"
- "employer": {
- "value": "Delta Marine Consultants PL"
- {
- "month": {
- "value": "2018-01"
- "employer": {
- "value": "Delta Marine Consultants PL"
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "cpfbalances": {
- "ma": {
- "value": 11470.71
- "oa": {
- "value": 1581.48
- "sa": {
- "value": 21967.09
- "ra": {
- "value": 0.01
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "vehicles": [
- {
- "vehicleno": {
- "value": "SDF1235A"
- "type": {
- "value": "PASSENGER MOTOR CAR"
- "iulabelno": {
- "value": ""
- "make": {
- "value": "TOYOTA"
- "model": {
- "value": "COROLLA ALTIS"
- "chassisno": {
- "value": "ZC11S1735800"
- "engineno": {
- "value": "M13A1837453"
- "motorno": {
- "value": ""
- "yearofmanufacture": {
- "value": "2010"
- "firstregistrationdate": {
- "value": "2010-06-06"
- "originalregistrationdate": {
- "value": "2010-06-06"
- "coecategory": {
- "value": "A - CAR UP TO 1600CC & 97KW (130BHP)"
- "coeexpirydate": {
- "value": "2020-06-05"
- "roadtaxexpirydate": {
- "value": "2020-06-05"
- "quotapremium": {
- "value": 14000.01
- "openmarketvalue": {
- "value": 25000.01
- "co2emission": {
- "value": 146.01
- "status": {
- "code": "1",
- "desc": "LIVE"
- "primarycolour": {
- "value": "BLACK"
- "secondarycolour": {
- "value": "WHITE"
- "attachment1": {
- "value": "DISABLED"
- "attachment2": {
- "value": "WITH SUN ROOF"
- "attachment3": {
- "value": "SIDE CURTAIN"
- "scheme": {
- "value": "REVISED OFF-PEAK CAR"
- "thcemission": {
- "value": 1.011001
- "coemission": {
- "value": 1.100001
- "noxemission": {
- "value": 0.011001
- "pmemission": {
- "value": 0.007
- "enginecapacity": {
- "value": 1600
- "powerrate": {
- "value": 1.41
- "effectiveownership": {
- "value": "2010-08-31T20:12:12+08:00"
- "propellant": {
- "value": "Compressed Natural Gas"
- "maximumunladenweight": {
- "value": 1500
- "maximumladenweight": {
- "value": 1795
- "minimumparfbenefit": {
- "value": 8770.01
- "nooftransfers": {
- "value": 2
- "vpc": {
- "value": "1234567890"
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
- "drivinglicence": {
- "comstatus": {
- "code": "Y",
- "desc": "ELIGIBLE"
- "totaldemeritpoints": {
- "value": 0
- "suspension": {
- "startdate": {
- "value": ""
- "enddate": {
- "value": ""
- "disqualification": {
- "startdate": {
- "value": ""
- "enddate": {
- "value": ""
- "revocation": {
- "startdate": {
- "value": ""
- "enddate": {
- "value": ""
- "pdl": {
- "validity": {
- "code": "V",
- "desc": "VALID"
- "expirydate": {
- "value": "2020-06-15"
- "classes": [
- {
- "class": {
- "value": "2A"
- {
- "class": {
- "value": "3A"
- "qdl": {
- "validity": {
- "code": "V",
- "desc": "VALID"
- "expirydate": {
- "value": "2020-06-15"
- "classes": [
- {
- "class": {
- "value": "2A"
- "issuedate": {
- "value": "2018-06-06"
- {
- "class": {
- "value": "3A"
- "issuedate": {
- "value": "2018-06-06"
- "photocardserialno": {
- "value": "115616"
- "classification": "C",
- "source": "1",
- "lastupdated": "2019-03-26"
